Blog
Posts, notes, and articles.
Software-Defined Networking: OpenFlow's Match-Action Tables, the P4 Language, and the Programmable Data Plane Vision
2026-04-15How SDN rewired the ossified internet architecture — from OpenFlow's match-action pipeline to P4's protocol-independent packet processing, and the ONOS/ODL control planes that orchestrate programmable forwarding at scale.
BGP and Internet Routing: The Path-Vector Protocol, AS-Level Topology, Convergence, and the Prefix Hijacking Problem
2026-04-08How BGP glues together 70,000+ autonomous systems into the global internet — the path-vector algorithm, route-flap damping, the convergence time problem, prefix hijacking, and the RPKI/BGPSec defenses that try to fix it.
QUIC and HTTP/3: The UDP-Based Transport Revolution — 0-RTT, Connection Migration, and Stream Multiplexing Without Head-of-Line Blocking
2026-03-06How QUIC rewrites the transport layer rulebook by moving TCP's reliability into userspace on top of UDP — 0-RTT handshakes, connection migration across IP addresses, and solving head-of-line blocking once and for all.

Content Delivery Networks: DNS-Based Routing, Anycast, Edge Caching, and the Economics of CDN Peering
2026-03-04How Akamai, Cloudflare, and Fastly keep the web fast — DNS-based request routing, anycast IPs, consistent hashing at the edge, and the business of CDN peering that makes it all economically viable.

Edge Computing: The Fog/Mist/Cloud Continuum, K3s, and the Computation Offloading Decision
2026-02-16How the edge-cloud continuum reshapes where computation happens — from K3s and MicroK8s for edge-native Kubernetes to 5G MEC, the offloading decision problem, and why latency and bandwidth dictate architecture at the edge.

Geo-Distributed Systems: WAN Latency, Multi-Leader Replication, and the Speed-of-Light Constraint
2026-02-13How the speed of light shapes the architecture of global-scale systems — from multi-leader and leaderless replication to CRDTs, Spanner, CockroachDB, and the fundamental tension between consistency and latency.

P2P Networks: BitTorrent's Incentives, IPFS's Merkle DAGs, and the Decentralized Web Vision
2026-01-18From tit-for-tat choking algorithms to content-addressed Merkle DAGs — how BitTorrent and IPFS engineered the two most successful decentralized protocols in internet history.
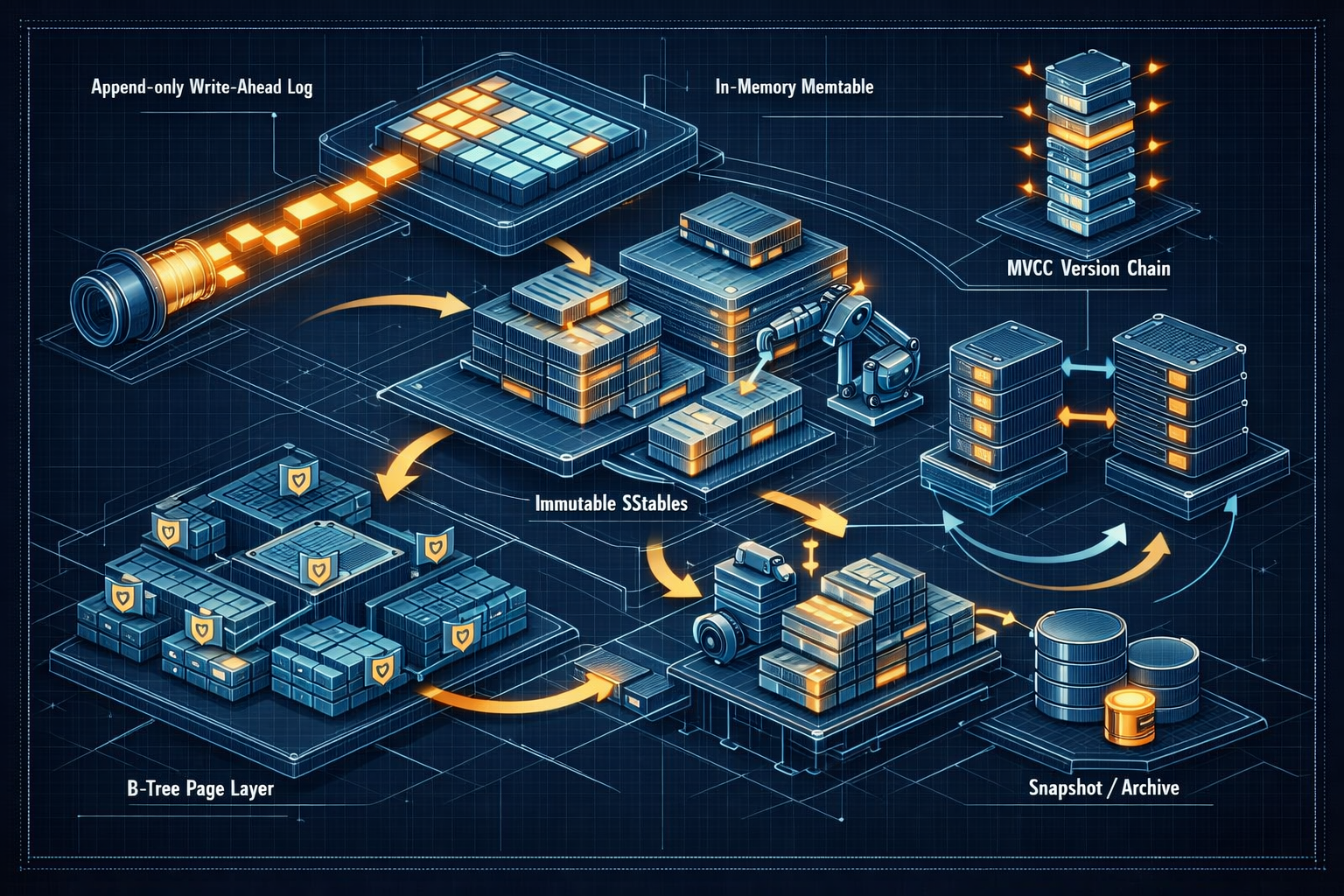
Database Internals: Storage Engines, Transactions, and Recovery
2025-12-21A deep technical walkthrough of how databases store data, ensure correctness, and recover from crashes — covering B-trees, LSM-trees, write-ahead logging, MVCC, isolation levels, and replication.

Distributed Hash Tables: Chord, Pastry, Kademlia, and the Structured Overlay Revolution
2025-12-08How consistent hashing, finger tables, prefix-based routing, and the XOR metric turned P2P networks from unscalable floods into efficient, provably correct structured overlays.
Epidemic Protocols: Gossip, HyParView, Plumtree, and the Mathematics of Infection-Style Dissemination
2025-12-08How push, push-pull, and pull gossip propagate information with tunable reliability guarantees — plus HyParView for membership and Plumtree for efficient broadcast in large-scale dynamic networks.
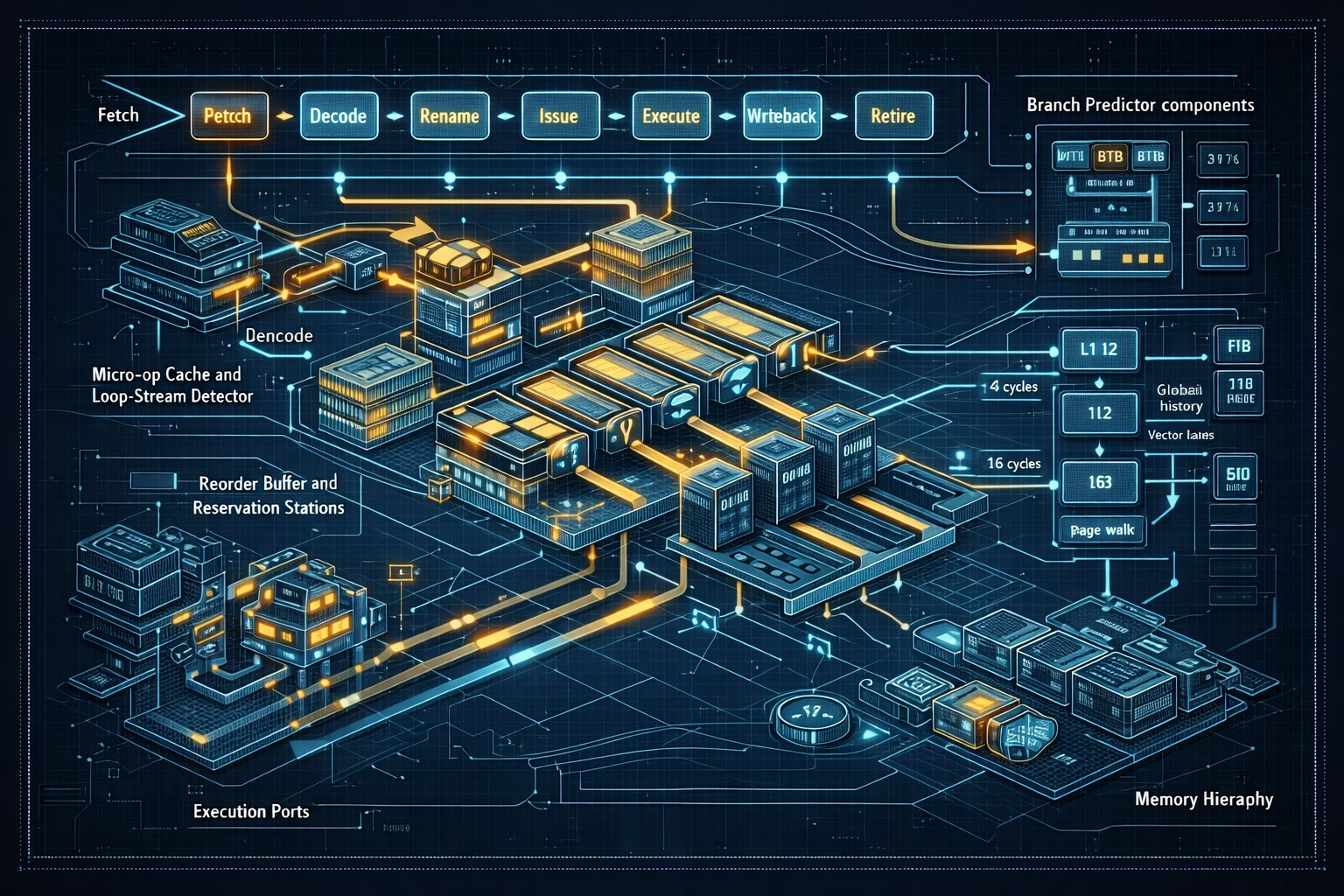
CPU Microarchitecture: Pipelines, Out-of-Order Execution, and Modern Performance
2025-12-04An in-depth exploration of CPU microarchitecture: instruction pipelines, hazards, branch prediction, out-of-order execution, register renaming, superscalar and SIMD units, and how software maps to hardware for performance.
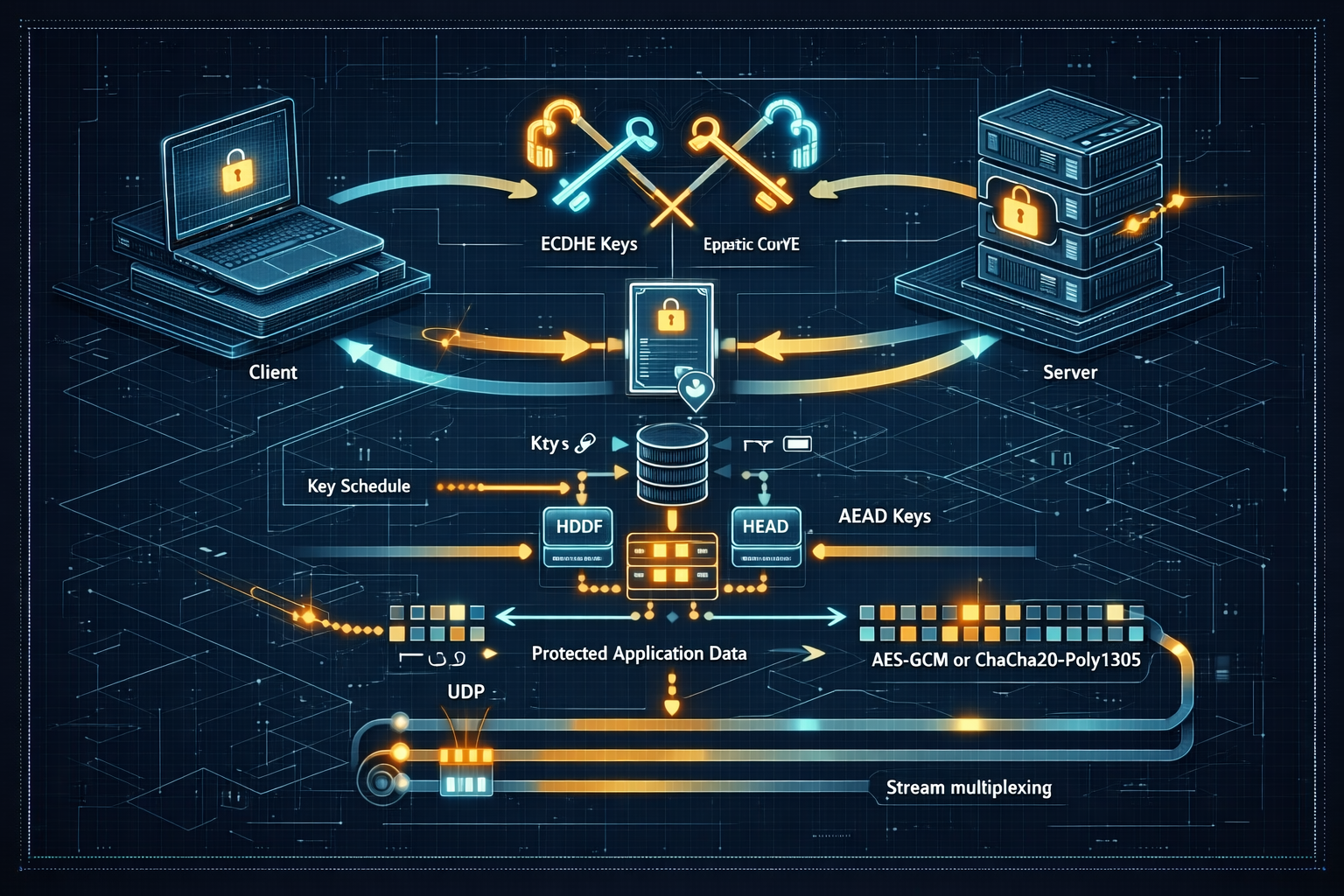
TLS, PKI, and Secure Protocols: How Encrypted Web Traffic Works
2025-11-18A deep technical guide to TLS, certificate validation, key exchange, record protection, modern cipher suites, TLS 1.3, QUIC, and practical deployment best practices for secure networked applications.

Distributed Snapshots: The Chandy-Lamport Algorithm, Lai-Yang, and the Foundations of Consistent Global State
2025-10-31How do you capture a consistent snapshot of a running distributed system without stopping the world? The Chandy-Lamport algorithm, its non-FIFO extension by Lai and Yang, and the deep connection to checkpointing and deadlock detection.

Inside Vector Databases: Building Retrieval-Augmented Systems that Scale
2025-10-26How modern vector databases ingest, index, and serve embeddings for production retrieval-augmented generation systems without falling over.
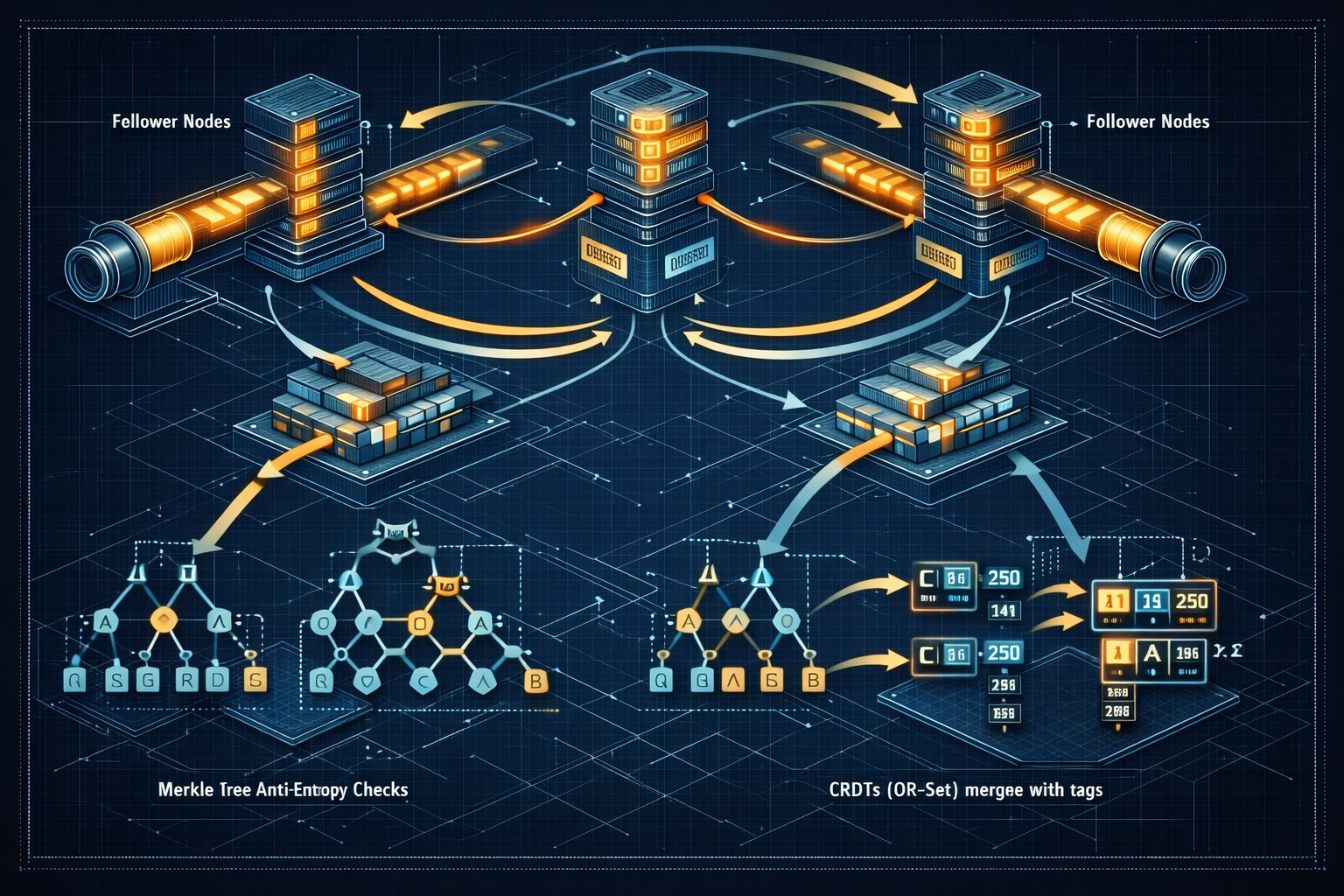
Distributed Systems: Consensus, Consistency, and Fault Tolerance
2025-10-20Fundamentals of distributed systems: failure models, consensus algorithms (Paxos, Raft), CAP theorem, consistency models, gossip, membership, CRDTs, and practical testing strategies like Jepsen.
Clock Synchronization: Lamport Clocks, Vector Clocks, Hybrid Logical Clocks, and the CRDT Connection
2025-10-08From scalar Lamport clocks that capture causality to vector clocks that characterize it precisely, through hybrid logical clocks that bridge physical and logical time — the intellectual lineage of distributed timekeeping.
Learned Indexes: When Models Replace B‑Trees
2025-10-04A practitioner's guide to learned indexes: how they work, when they beat classic data structures, and what it takes to ship them without getting paged.
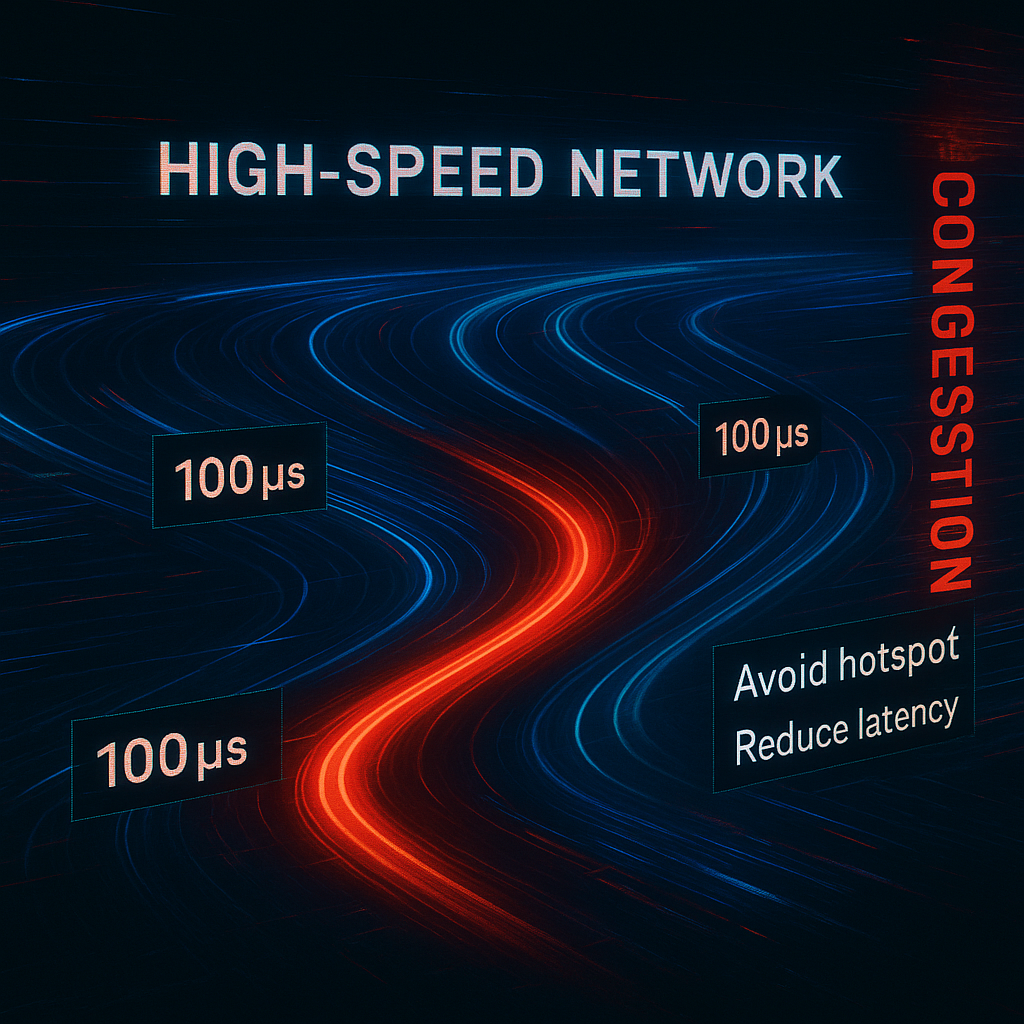
The 100‑Microsecond Rule: Why Tail Latency Eats Your Throughput (and How to Fight Back)
2025-10-04A field guide to taming P99 in modern systems—from queueing math to NIC interrupts, from hedged requests to adaptive concurrency. Practical patterns, pitfalls, and a blueprint you can apply this week.

Time in Distributed Systems: NTP, PTP, TrueTime, and the Impossibility of Perfect Synchronization
2025-10-01From Marzullo's algorithm in NTP to hardware timestamping in PTP and Google's TrueTime in Spanner — how distributed systems wrestle with the fundamental impossibility of perfectly synchronized clocks.
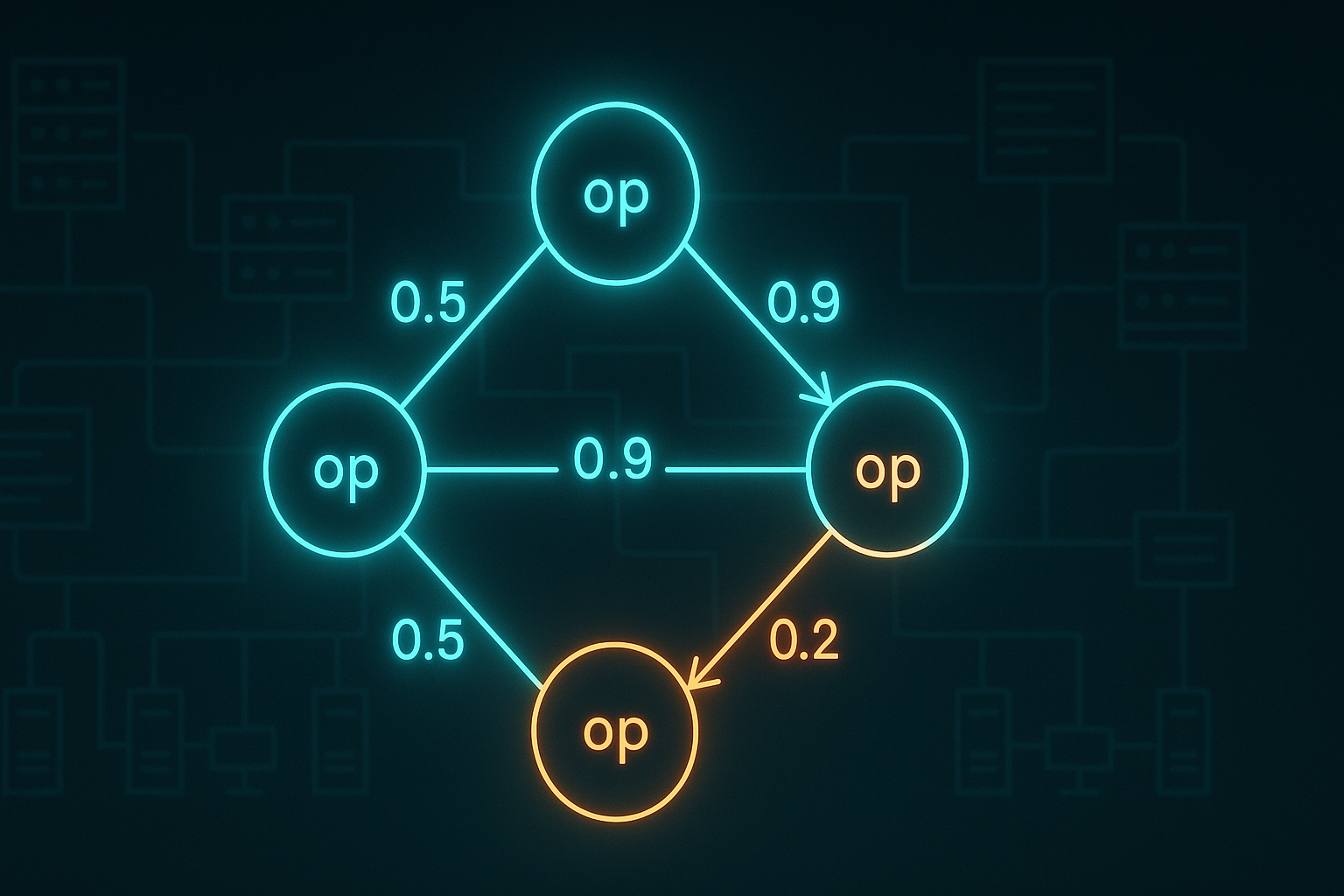
The Quiet Calculus of Probabilistic Commutativity
2025-09-27A practical calculus for quantifying when non-commutative operations in distributed systems can be safely executed without heavyweight coordination.
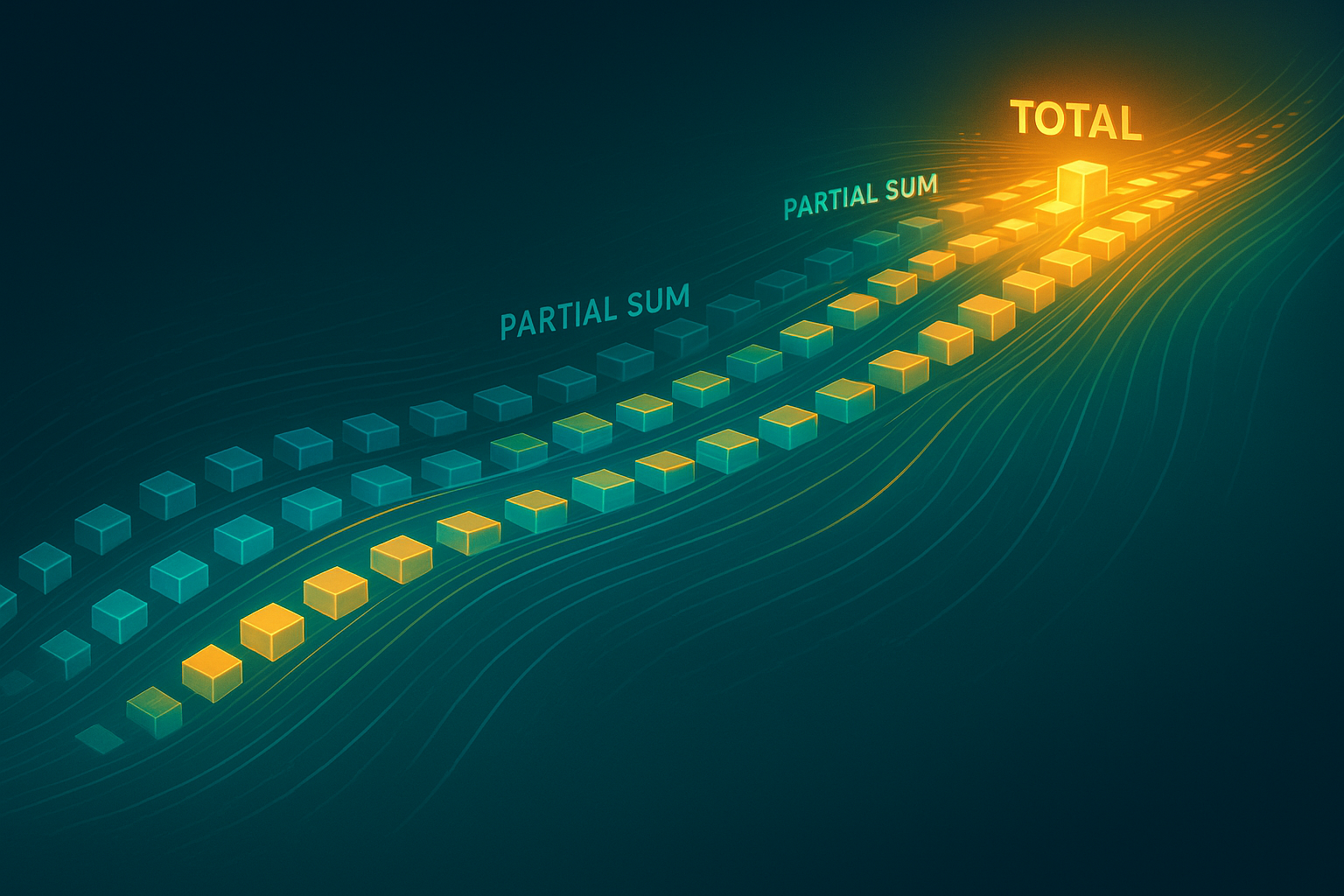
The Hidden Backbone of Parallelism: How Prefix Sums Power Distributed Computation
2025-09-21Discover how the humble prefix sum (scan) quietly powers GPUs, distributed clusters, and big data frameworks—an obscure but essential building block of parallel and distributed computation.
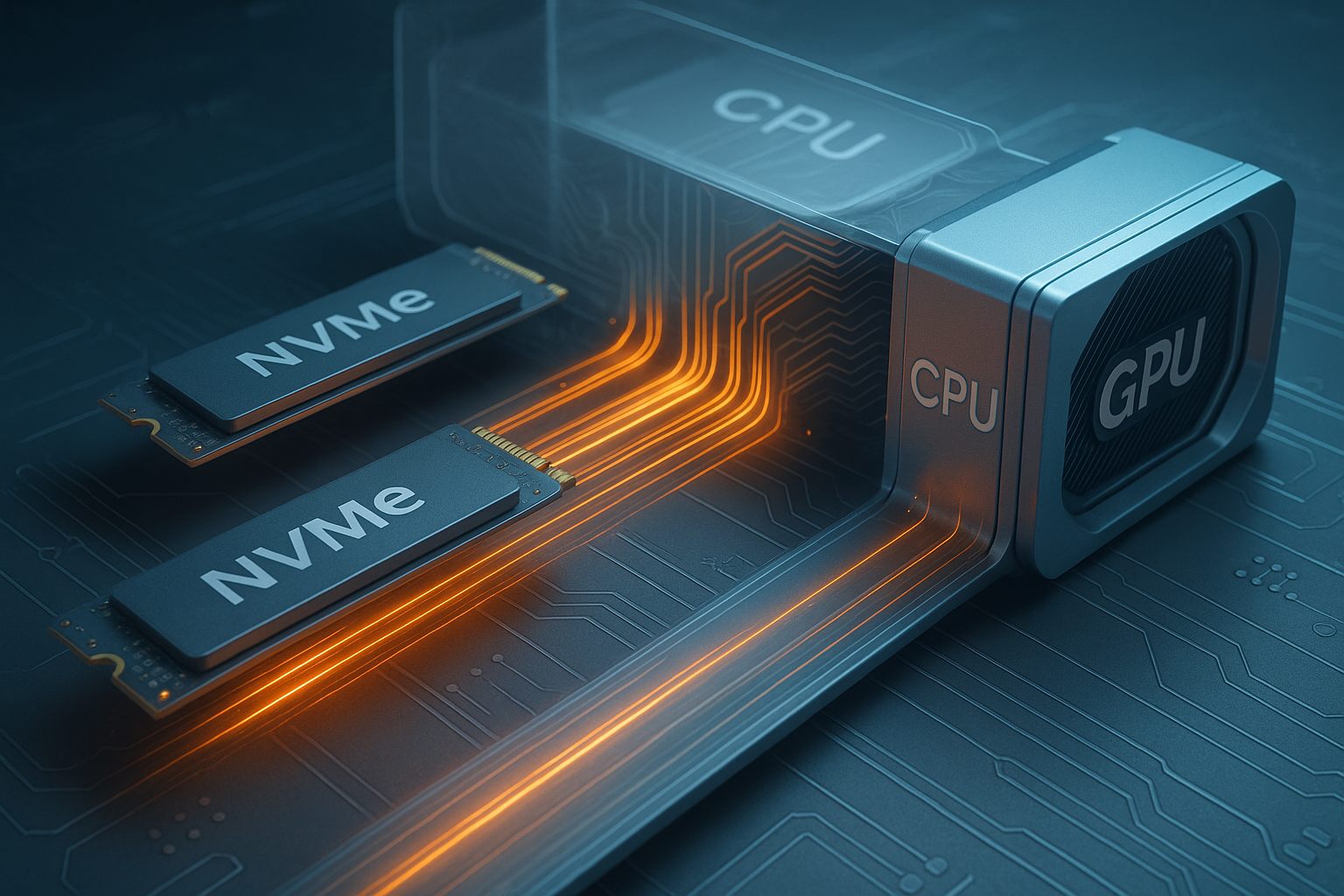
GPUDirect Storage in 2025: Optimizing the End-to-End Data Path
2025-09-16How modern systems move data from NVMe and object storage into GPU kernels with minimal CPU overhead and maximal throughput.

The Johnson-Lindenstrauss Lemma and the Geometry of High-Dimensional Data
2025-09-05Explore the surprising geometry of high-dimensional spaces: the Johnson-Lindenstrauss lemma showing that random projections preserve pairwise distances, the concentration phenomena that make it work, and its profound applications in nearest-neighbor search, compressed sensing, and machine learning.

Lattice-Based Cryptography: Learning With Errors and the Road to Fully Homomorphic Encryption
2025-08-24Enter the post-quantum world of lattice-based cryptography: the Learning With Errors (LWE) problem, its reduction from worst-case lattice problems, the construction of basic encryption from LWE, and the stunning breakthrough of fully homomorphic encryption that computes on encrypted data.